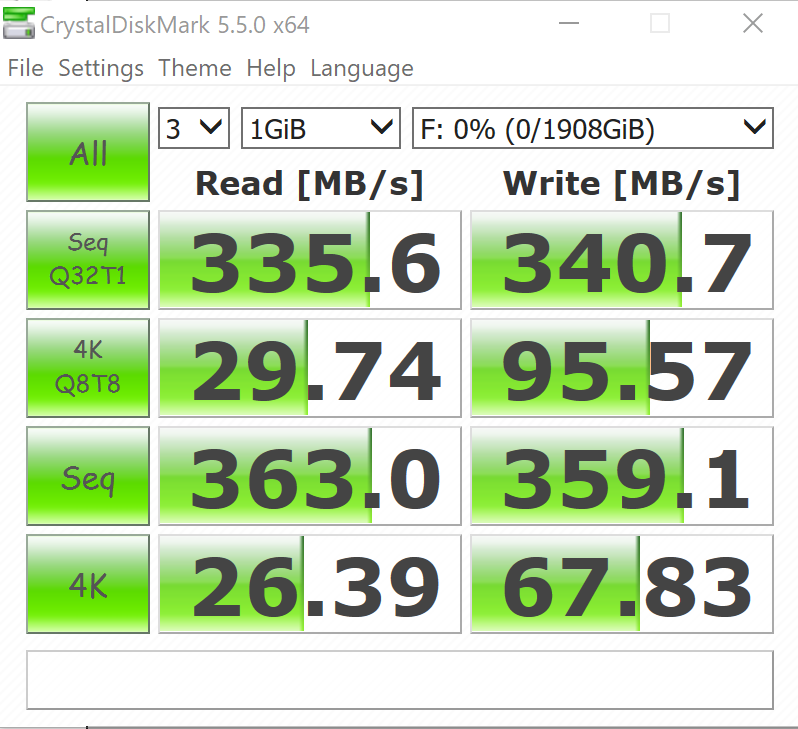
CRYSTAL DISK BENCHMARK VER. 5.5.0 X64
Crystal Disk Benchmark is used to measure read and write performance through sampling of random data which is, for the most part, incompressible. Performance is virtually identical, regardless of data sample so we have included only that using random data samples.
As much as we might like to see the low 4K performance a bit higher, this remains to be a very good result for an encrypted SSD.
The toughest benchmark available for solid state drives is AS SSD as it relies solely on incompressible data samples when testing performance. For the most part, AS SSD tests can be considered the ‘worst case scenario’ in obtaining data transfer speeds and many enthusiasts like AS SSD for their needs. Transfer speeds are displayed on the left with IOPS results on the right.The AS SSD results aren’t as appealing as we might like to see but do get a first look at read and write IOPS which appear to be in the general ball park of listed specs.
ANVIL STORAGE UTILITIES PROFESSIONAL
Anvil’s Storage Utilities (ASU) are the most complete test bed available for the solid state drive today. The benchmark displays test results for, not only throughput but also, IOPS and Disk Access Times. Not only does it have a preset SSD benchmark, but also, it has included such things as endurance testing and threaded I/O read, write and mixed tests, all of which are very simple to understand and use in our benchmark testing.
TxBench is one of our newly discovered benchmarks that we works much the same as Crystal Diskmark, but with several other features. Advanced load benchmarking can be configured, as well as full drive information and data erasing via secure erase, enhanced secure erase, TRIM and overwriting. Simply click on the title for a free copy.
AJA VIDEO SYSTEM DISK TEST
The AJA Video Systems Disk Test is relatively new to our testing and tests the transfer speed of video files with different resolutions and Codec.
 The SSD Review The Worlds Dedicated SSD Education and Review Resource |
The SSD Review The Worlds Dedicated SSD Education and Review Resource | 

One thing it lacks is physical security.
Page 18 of the User Manual says:
Performing a Complete Reset
NOTE: A complete reset will erase encryption keys and PINs and leave the Aegis Fortress
in an unformatted condition.
There may be circumstances (forgotten PIN, redeployment, return to factory default
settings) when you need to completely reset the drive. The complete reset feature will
perform a crypto-erase on the drive, generate a new encryption key, delete all users, and
return all of the settings to factory default.
To perform a complete reset of the drive, perform the following:
1. Press and hold ? + ? + 2 together for several seconds. The RED and BLUE LEDs
will blink alternately.
2. Release all buttons when the GREEN and RED LEDs glow steadily which will
continue for several seconds, followed by the GREEN LED glowing steadily for
several seconds, and then will be followed finally by the GREEN and BLUE LEDs
glowing steadily, indicating that the reset is complete.
3. A new Admin PIN will need to be entered and the drive will need to be reformatted.
So you can steal it, erase it, reset it, and use it as if you had purchased it yourself (minus the Warranty).
we actually talk about this now and then. and yeah that’s true. and it’s true for most other manufacturers who don’t have a device management console or a software component. we thought about it a lot and opted to stick with a non managed system to allow us to lock down the firmware and eliminate update opportunities because that’s a malware vulnerability occurs and also, it’s hackable. the real concern that we focus on is the security of your data on the drive. when the average data breach cost gets up over 3 million in damages and fines, we figure you’d rather be out a few hundred bucks in the loss of the drive itself and get another one.
Thank you for jumping in Apricorn.
Couldn’t the first key entered be the ‘user lock’ for the drive, unneeded until next time a complete reset is performed?
After a complete reset one would have to enter the first key ever used, otherwise it would be a brick.
Another method would be a peel-off sticker unrelated to the serial number which contains the key to use.
Some of the drives are more than a few hundred dollars and while some might steal it thinking it had value those in the know would understand that the only “value” would be to cause concern and deprive the user of the data (which could cost thousands of dollars).
It’s like leaving your vehicle unlocked so the thief doesn’t confront you in the parking lot and take your keys – instead all vehicles have locks (some encrypted) and most people lock their cars, car jackings are infrequent (plus there’s OnStar and LoJack, no suggestion that you add it).
Thanks for answering, all the same.