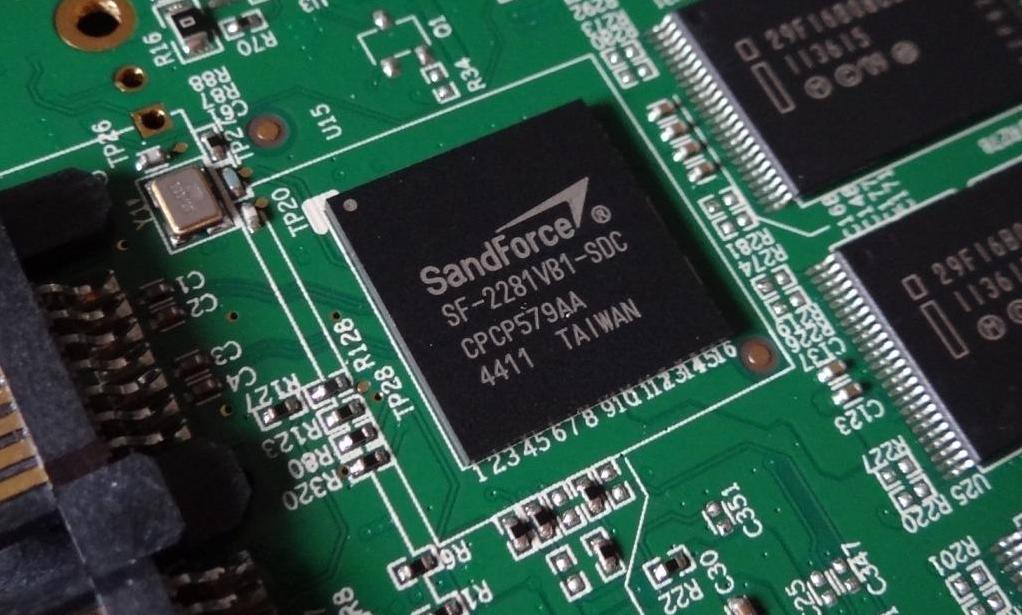
An internal security audit by LSI discovered that the world famous SandForce 256-bit AES encryption of LSI Flash Storage Processors (FSP) has never been, and is not presently enabled in SandForce SSDs, as stated by LSI SandForce representatives today.
Fret not, however, as 128-bit encryption is still in place and, unique to SandForce, the SandForce SSDs are the only ones to have two separate encryption engines, a 256-bit engine on the front end and another 128-bit engine on the back end. It is the front end 256-bit engine that currently works at only 128-bit encryption, however.
The entire situation is rather an interesting story because it is based on requirements where the US government restricts the export of any hardware to certain countries, as a matter of national security, if they contain 256-bit AES security encryption. It is for this reason that all SF-2000 processors needed to be configurable to the less controlled 128-bit encryption and this not only contributes, but just may be the reasoning behind the 256-bit encryption engine not working. Fortunately the 128-bit AES Security Encryption engines are there to ensure complete security is in place in just this type of situation.
AES ENCRYPTION EXPLAINED
To try and break things down for the laymen, Wikipedia describes AES as a type of encryption where the same key is used to encrypt and decrypt the data and has been adopted by the US government and used worldwide. AES operates on a 4×4 column-major order matrix of bytes, termed the state. Most AES calculations are done in a special finite field.
The AES cipher is specified as a number of repetitions of transformation rounds that convert the input plaintext into the final output of ciphertext. The number of cycles of repetition are as follows:
10 cycles of repetition for 128-bitkeys.
12 cycles of repetition for 192 bit keys.
14 cycles of repetition for 256-bit keys.
In an amusing analogy, I remember a statement once where it was compared that it would take a billion monkeys billions of years to break 128-bit code. So add to that the fact that the LSI SandForce processor has both a front and back end encryption engine making it even more secure without the 256-bit encryption.
There is a saving grace in all which adds decidedly to the credibility of LSI and that is that they are continually doing validation testing and, not only ensuring all is in order, but are resolving any issues immediately and notifying what has become a total of fifty partners worldwide. We will, of course, see updates roll out by each in the near future, however, the details of this timing cannot be confirmed nor denied by LSI SandForce directly as a result of non-disclosure agreements in place.
SSD MANUFACTURERS OFFER DIFFERENT SOLUTIONS
Since our original post, we have received similar releases from manufacturers remedying the situation to various degrees. Intel is offering a full refund to customers who purchased a 520 Series SSD before 1 July 2012 and they must contact Intel customer support prior to 1 October 2012. With respect to Kingston, it affects the SSDNow V+200 and KC100 lines of SSDs and they provide that they are working closely with LSI SandForce to make work towards a solution and customers are welcome to call customer support for assistance and exchange once new drives become available.
Manufacturer releases will be posted on subsequent pages, as they arrive, and our initial release was not the result of a release, but rather, conversation with LSI directly.
 The SSD Review The Worlds Dedicated SSD Education and Review Resource |
The SSD Review The Worlds Dedicated SSD Education and Review Resource | 
That statement about ..monkeys!!! I loved it
Looks like Intel is offering to exchange 520 128 AES drives for 256 when they come available or refund full purchase price! Doubt Ocz will do the same tho…
Does OCZ have SF-models with encryptions enabled?
https://www.ocztechnologyforum.com/forum/showthread.php?102264
OCZ statement so far (at least on their international board, nothing on the German one so far)
The error or bug was found by Intel on there yearly audit, not LSI, Intel are giving returns, in there specifications they state both encryption states, and they sell a lot of these drives to companies who require good encryption, all I’ve seen so far from LSI is excuses.
According to Sandforce, you need to set a password for the encryption to work anyway and they consider 95% of users don’t use it anyway and OCZ at some time or other have advertised the 256 bit encryption so the email is also a excuse.
If both OCZ and Sandforce new about the limitation, they kept there mouths firmly closed. If they didn’t, fair enough. Sorry Les not sure I agree with you or LSI on this one.
PommieB
I spoke with LSI in the initial interview and then subsequent to the Intel release and was told it was a LSI discovery. I might have thought if Intel had discovered it they would have ramrodded the initial release and not been held back until the LSI release. To this point, there is no discussion by anyone with Intel other than there release, whereas, I spoke with LSI at length about this under NDA.
No offense meant Les and I can understand why you would have that opinion, the fact that Sandforce drives didn’t have the advertised 256bit encryption didn’t worry me at all, even LSI statement, I found it rather amusing actually, ( I wish my x-wife gave me statements like that, I’d have known about the affair she was having behind my back ) I read this report when you first published it. What annoyed me was the link made by OCZ, I’m sure LSI discovered and notified OCZ who removed the 256bit encryption from there specs.
Had OCZ not made that statement, I wouldn’t have given your report a second glance, it looks to me that both LSI and OCZ knew beforehand that the 256bit encryption didn’t work and they didn’t consider it important enough to at least notify Intel or the other manufacturers that it didn’t work.
You are right, we are never going to know the true story and it is a storm in a teacup to most manufacturers, but obviously not in Intel’s case. But hey! who would you have to argue with if I wasn’t around. Best of luck Mate.
PommieB
Never an argument with you Pommie and we go back a long way now. I appreciate you visiting and jumping in here when you have the opportunity and have to concede that it would be great to see your presence here.
I wonder what, if anything, OWC offers. They make nothing but SandForce-based SSD’s.
256 Bit encryption has been proven to be less secure than 128 bit. Add to that the fact that, unlike other manufacturers, LSI SandForce has encryption engines on both sides of the data and the fact that very few even use 256 Bit. Most manufacturers have simply not jumped in to respond because this isn’t as bif of a story as most would like it to be.
It goes to show how much more Intel stands behind its products 100%, as compared to XXX, for example. They still list “256-bit chip-based encryption” on their site as of 6/24/12 @ 4:23pm PT.
I appreciate your response and have edited out the specific manufacturer as your point led me to check others to which I found the same. Interesting…
Apologies if it offends in any way but I believe the point is best served without ‘targeting’ if I might mention it in that way. Tx!
So if I buy a SSD with a SandForce SF-2281 controller with no intentions of using encryption, is there anything I need to be concerned about in regards to this?
Absolutely none, and in fact, you have to wonder how many were utilizing such, or had knowledge of its not being in use, as it took so long to identify this.
I heard lot about; that OCZ also comes with encryption
model I tried to search on the Internet as well but can’t find anything strong related
to it. Do you know anything about it ?
When we speak of encryption, I think we are speaking only to the same encryption that is available in all SandForce controllers which includes some OCZ models.